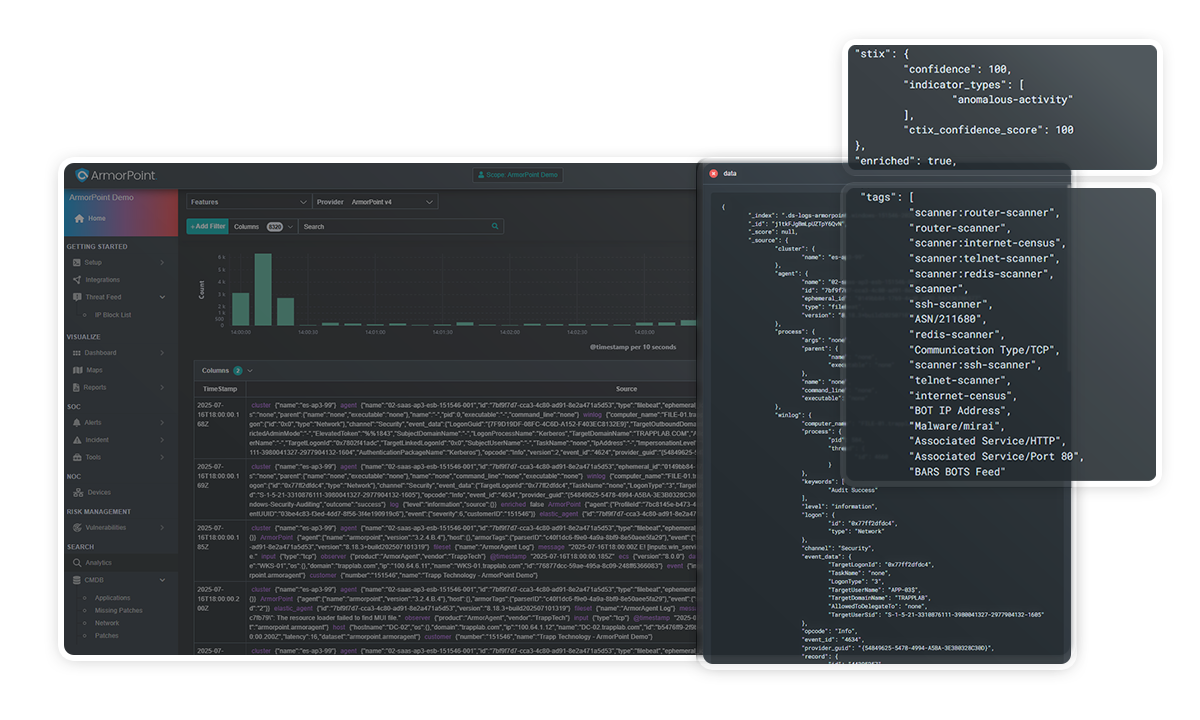
The SIEM Platform
You Don’t Have to Manage.
With ArmorPoint Managed SIEM, cut through the noise, reduce resource strain, and gain 24/7 visibility and control with a SIEM + SOC solution purpose-built for lean IT and security teams.
ArmorPoint Managed SIEM Use Cases
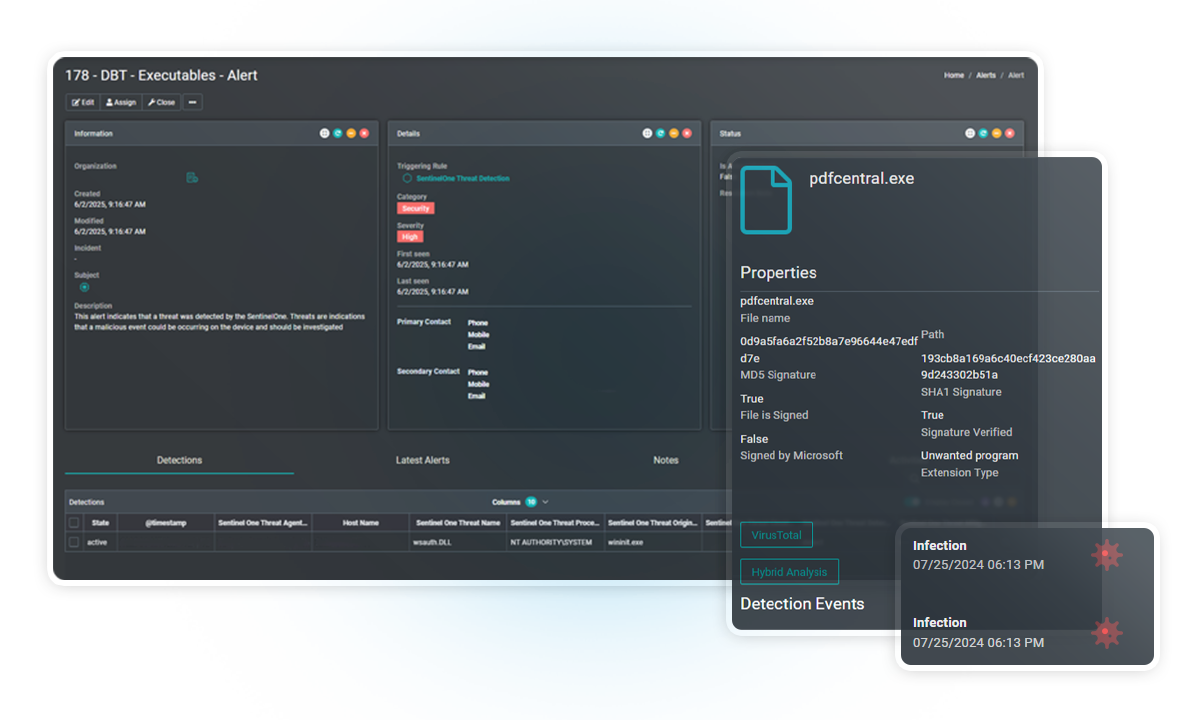
Malware Detection
Detect and respond to known and unknown malware through behavior-based analysis, threat intelligence correlation, and automated alerting. ArmorPoint analyzes system activity and file behavior across your environment to identify indicators of compromise (IoCs).
Key Features:
- Correlation with threat intelligence feeds (commercial + open-source)
- Detection of suspicious binaries, command-and-control activity, and lateral movement
- Custom rule creation for environment-specific threats
- 24/7 SOC alert validation and triage
File Integrity Monitoring
Monitor critical Linux system files and directories for unauthorized changes. ArmorPoint’s FIM capability ensures the integrity of essential assets by generating alerts on unexpected file modifications, deletions, or permission changes.

Key Features:
- Real-time file change monitoring for Linux-based systems
- Baseline comparison and hash verification
- Alerting on unauthorized changes to binaries, configurations, or scripts
- Logging and reporting for compliance use cases (e.g., PCI DSS, HIPAA)
- Integration with audit policies and system agents
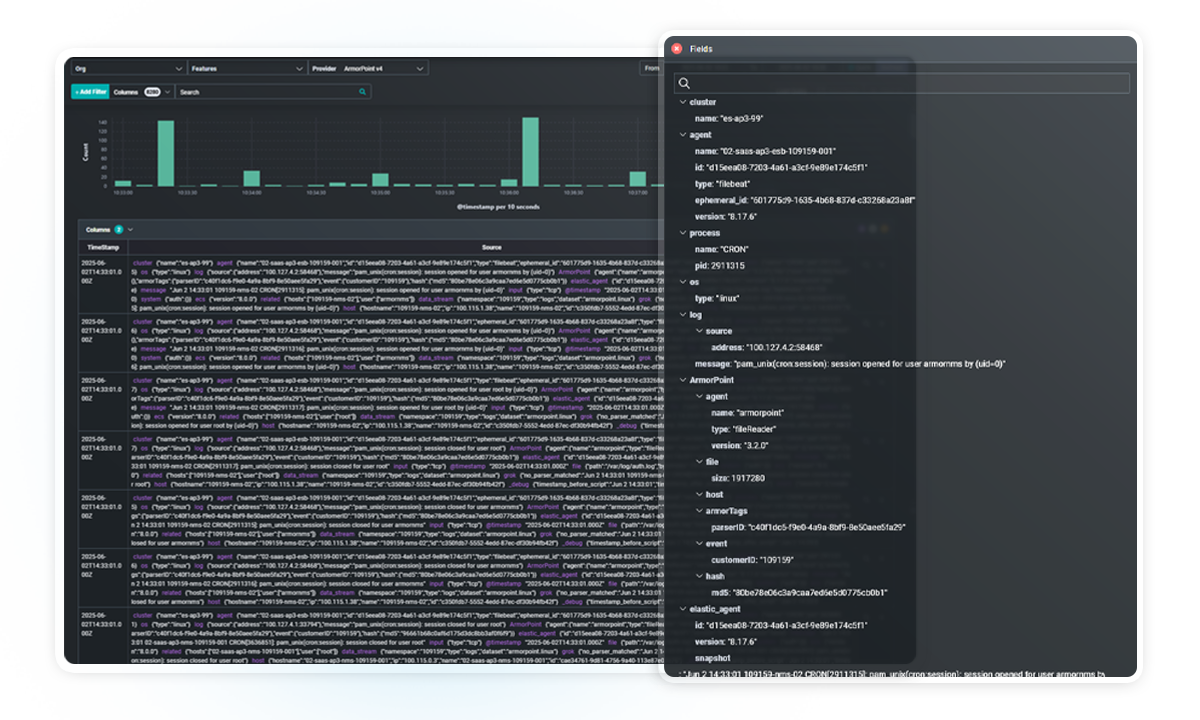
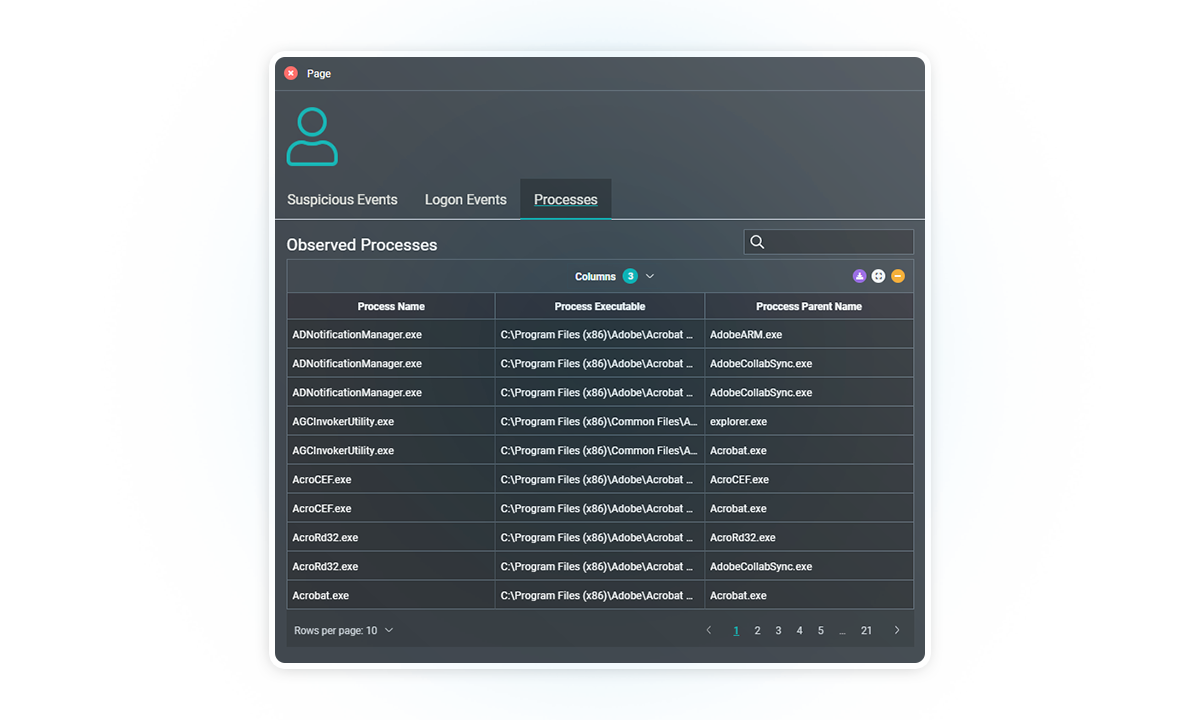
Threat Hunting
Enable proactive threat discovery using historical and real-time event data. ArmorPoint allows security teams to perform guided and custom investigations across log sources, helping uncover indicators of advanced persistent threats (APTs) or stealthy behaviors.

Key Features:
- Access to raw and enriched telemetry across all connected data sources
- Query-based searches and correlation rule tuning
- Support for hypothesis-driven and behavior-based investigations
- Historical data analysis for retroactive threat discovery
- Analyst-backed threat validation and contextual enrichment
Log Data Analysis
Centralize, parse, and correlate log data across diverse environments to support detection, compliance, and operational insight. ArmorPoint ensures structured visibility and operational awareness.
Key Features:
- Unlimited ingestion and retention of log files (hot and cold storage)
- Support for custom log types and formats (e.g., SSHGuard, IIS/Apache)
- Automatic parsing and normalization across data sources
- Searchable log archive with advanced filtering
- Integrated dashboards for KPI and anomaly visualization
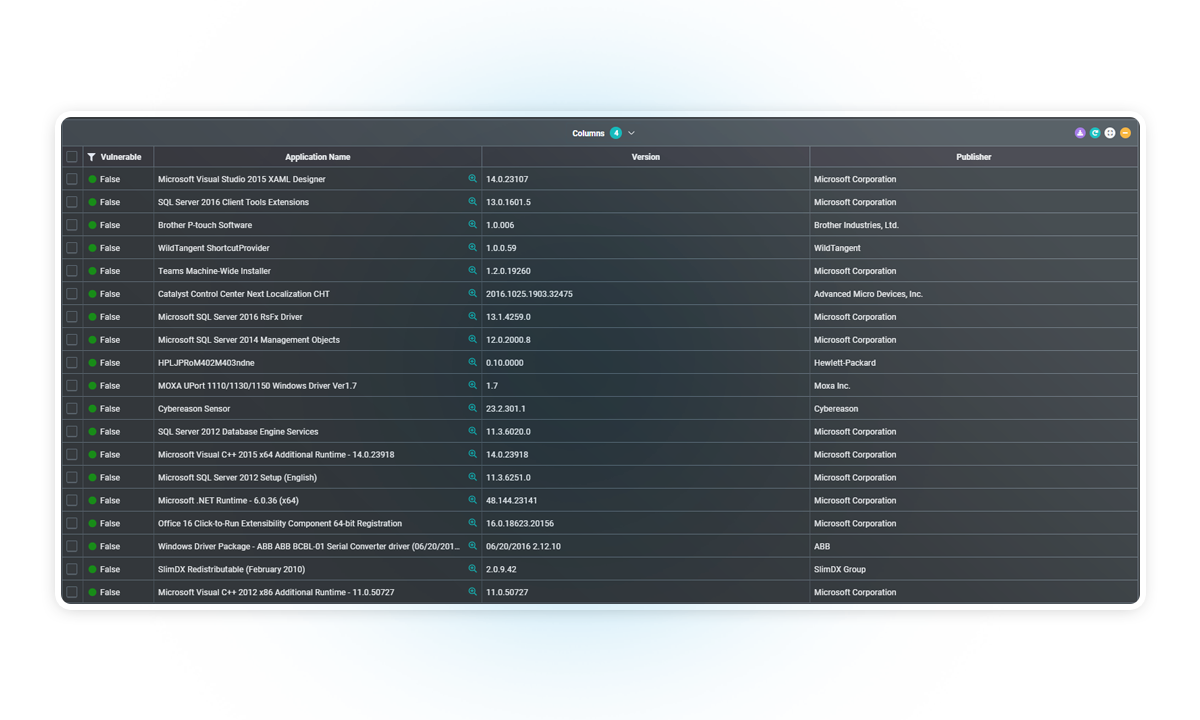
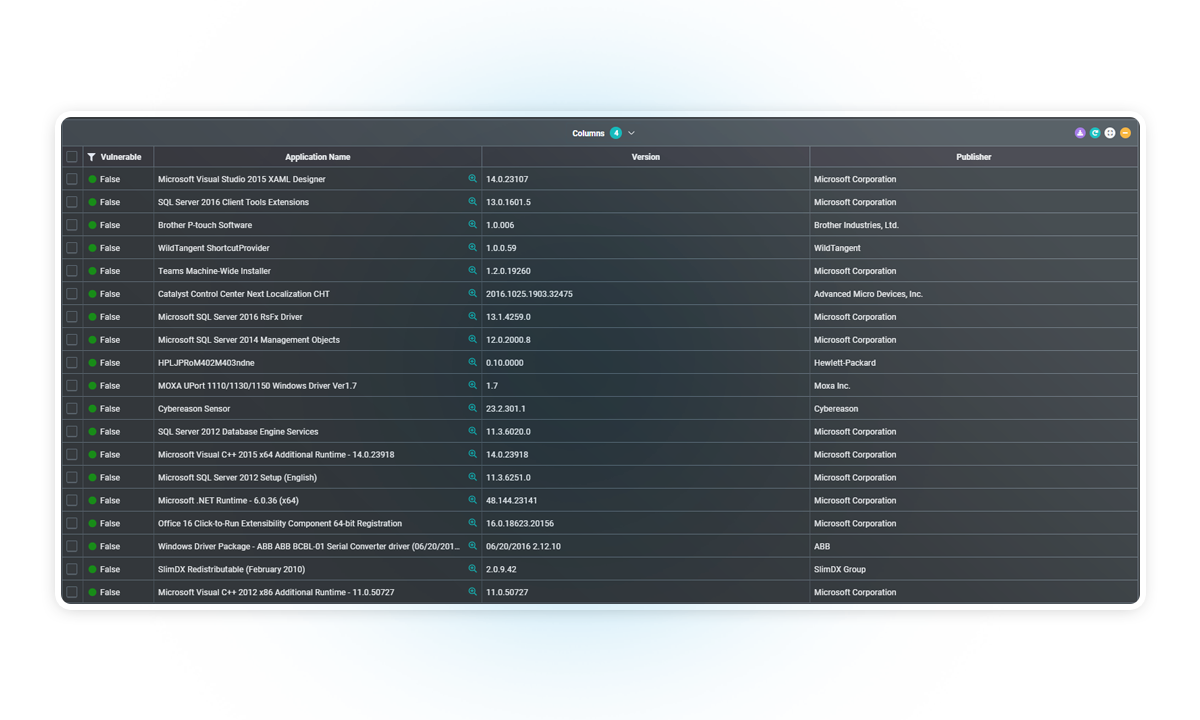
Vulnerability Detection
Continuously assess assets for known vulnerabilities and misconfigurations. ArmorPoint identifies security gaps and prioritizes findings based on severity, exploitability, and relevance to your environment.

Key Features:
- Integration with vulnerability scanners and external asset data
- Mapping of CVEs to log and system activity
- Alerting on exposure to active exploit campaignsCustom rule creation for environment-specific threats
- Cross-correlation with threat intel for prioritization
- Audit reporting for patch management and remediation tracking
Incident Response
Support rapid investigation and coordinated response to threats. ArmorPoint’s managed SOC service includes incident triage and guidance to contain or mitigate threats before they escalate.

Key Features:
- Real-time alerting with SOC-led triage and escalation
- Incident tracking and timeline generation
- Recommendations for containment and remediation
- SLT-backed response procedures
- Integration with mobile app for on-the-go response
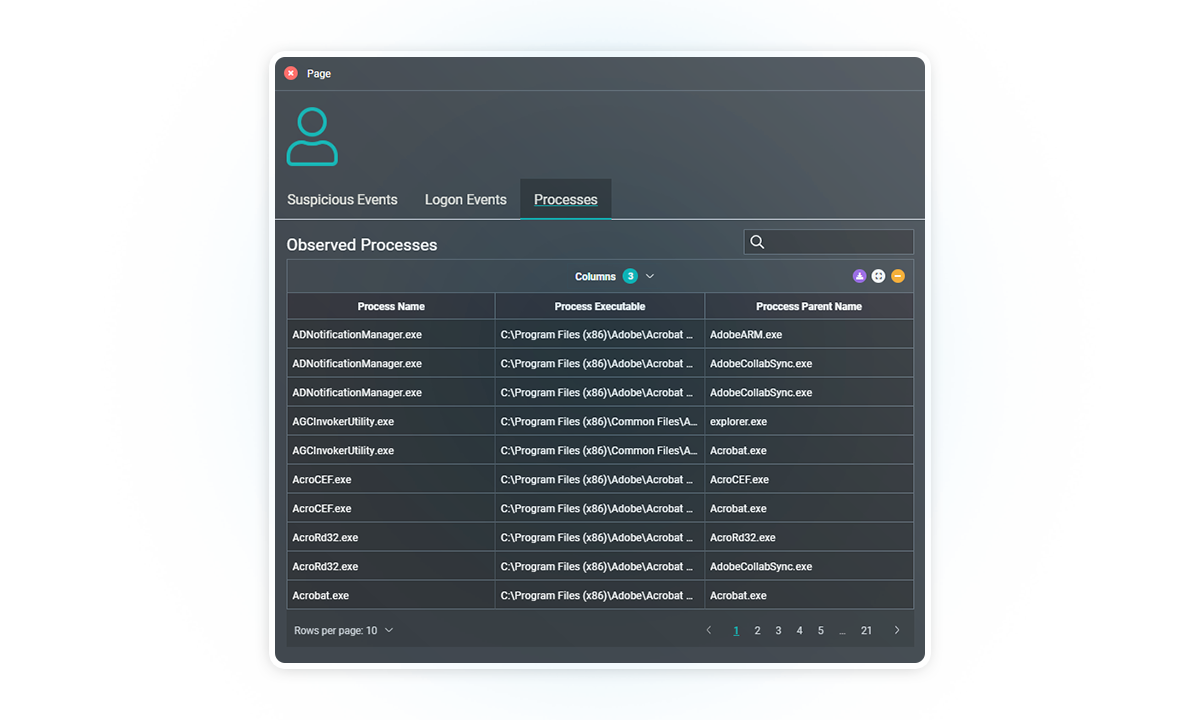
IT Hygiene
Maintain system integrity and enforce security best practices through continuous monitoring. ArmorPoint helps ensure proper configurations, user behaviors, and system policies are upheld across your infrastructure.
Key Features:
- Detection of insecure configurations and access anomalies
- Monitoring of dormant accounts, privileged access, and usage spikes
- Policy-based compliance validation (CIS benchmarks, NIST guidance)
- Automated alerts on misconfigured logging or disabled monitoring
- Environment-wide visibility for hygiene status reporting
Workload Protection
Extend detection and monitoring capabilities to cloud-native, hybrid, and on-prem workloads. ArmorPoint secures workloads against unauthorized access, suspicious activity, and privilege escalation.
Key Features:
- Log collection and correlation across VMs and cloud services
- Monitoring of lateral movement and inter-workload communication
- User activity auditing within workload boundaries
- Integration with AWS, Azure, and GCP environments
- Alerts on anomalous process execution or configuration drift
Posture Management
Continuously evaluate your organization’s security posture and reduce risk exposure through unified monitoring, detection, and compliance alignment.

Key Features:
- Centralized visibility into security operations and control gaps
- Customizable dashboards with posture metrics
- Event correlation tied to security policy violations
- Support for control assessments and audit preparation
- Ongoing alignment with internal governance and external frameworks
Threat Intelligence
Enhance detection accuracy and accelerate response with built-in threat intelligence. ArmorPoint enriches every event with context from commercial and open-source feeds, giving security teams the intel they need to prioritize and respond with confidence without additional licensing or subscription costs.
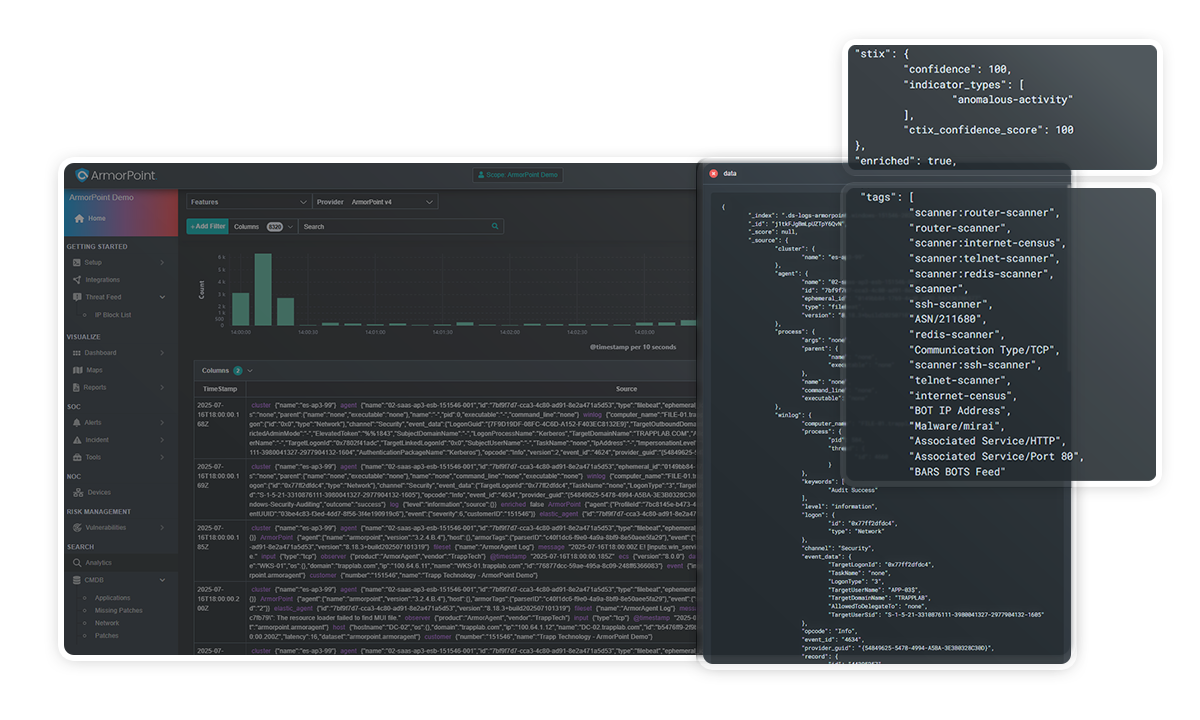
Key Features:
- Integration of multiple commercial and open-source threat intelligence feeds
- Automatic enrichment of logs and alerts with IOCs, IP reputation, malware signatures, and more
- Real-time correlation between internal events and external threat indicators
- Support for threat scoring, tagging, and prioritization
Malware Detection
Detect and respond to known and unknown malware through behavior-based analysis, threat intelligence correlation, and automated alerting. ArmorPoint analyzes system activity and file behavior across your environment to identify indicators of compromise (IoCs).
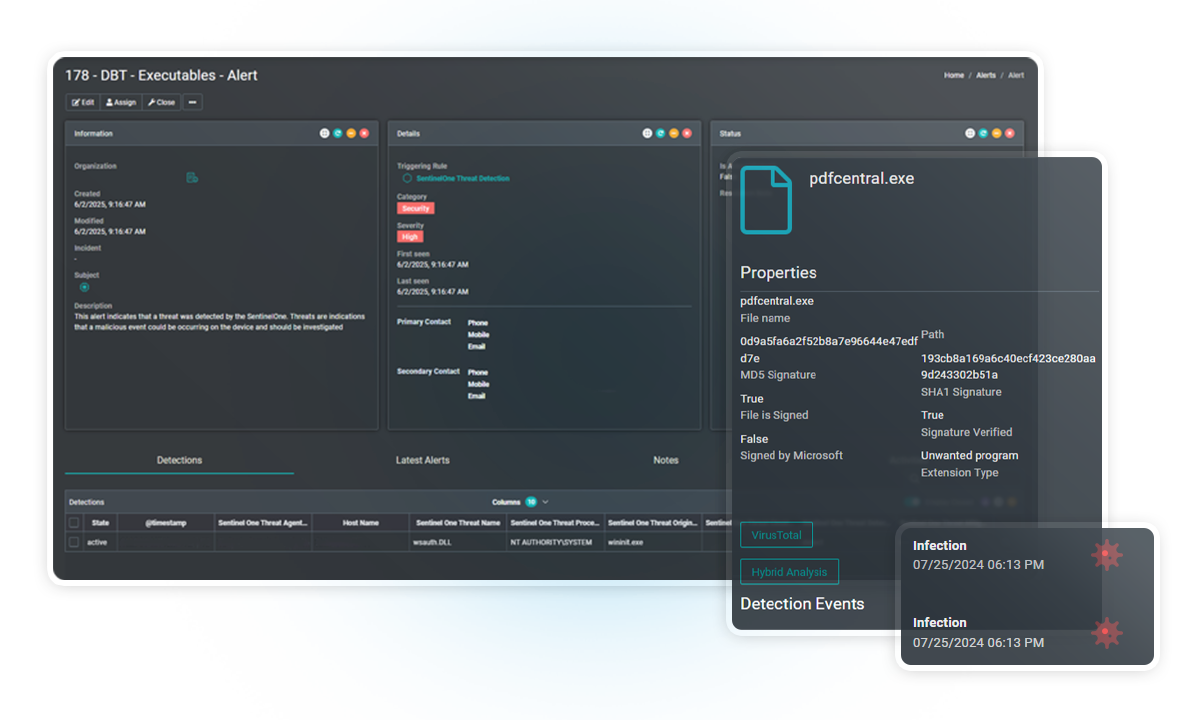
Key Features:
- Correlation with threat intelligence feeds (commercial + open-source)
- Detection of suspicious binaries, command-and-control activity, and lateral movement
- Custom rule creation for environment-specific threats
- 24/7 SOC alert validation and triage
File Integrity Monitoring
Monitor critical Linux system files and directories for unauthorized changes. ArmorPoint’s FIM capability ensures the integrity of essential assets by generating alerts on unexpected file modifications, deletions, or permission changes.

Key Features:
- Real-time file change monitoring for Linux-based systems
- Baseline comparison and hash verification
- Alerting on unauthorized changes to binaries, configurations, or scripts
- Logging and reporting for compliance use cases (e.g., PCI DSS, HIPAA)
- Integration with audit policies and system agents
Threat Hunting
Enable proactive threat discovery using historical and real-time event data. ArmorPoint allows security teams to perform guided and custom investigations across log sources, helping uncover indicators of advanced persistent threats (APTs) or stealthy behaviors.

Key Features:
- Access to raw and enriched telemetry across all connected data sources
- Query-based searches and correlation rule tuning
- Support for hypothesis-driven and behavior-based investigations
- Historical data analysis for retroactive threat discovery
- Analyst-backed threat validation and contextual enrichment
Log Data Analysis
Centralize, parse, and correlate log data across diverse environments to support detection, compliance, and operational insight. ArmorPoint ensures structured visibility and operational awareness.
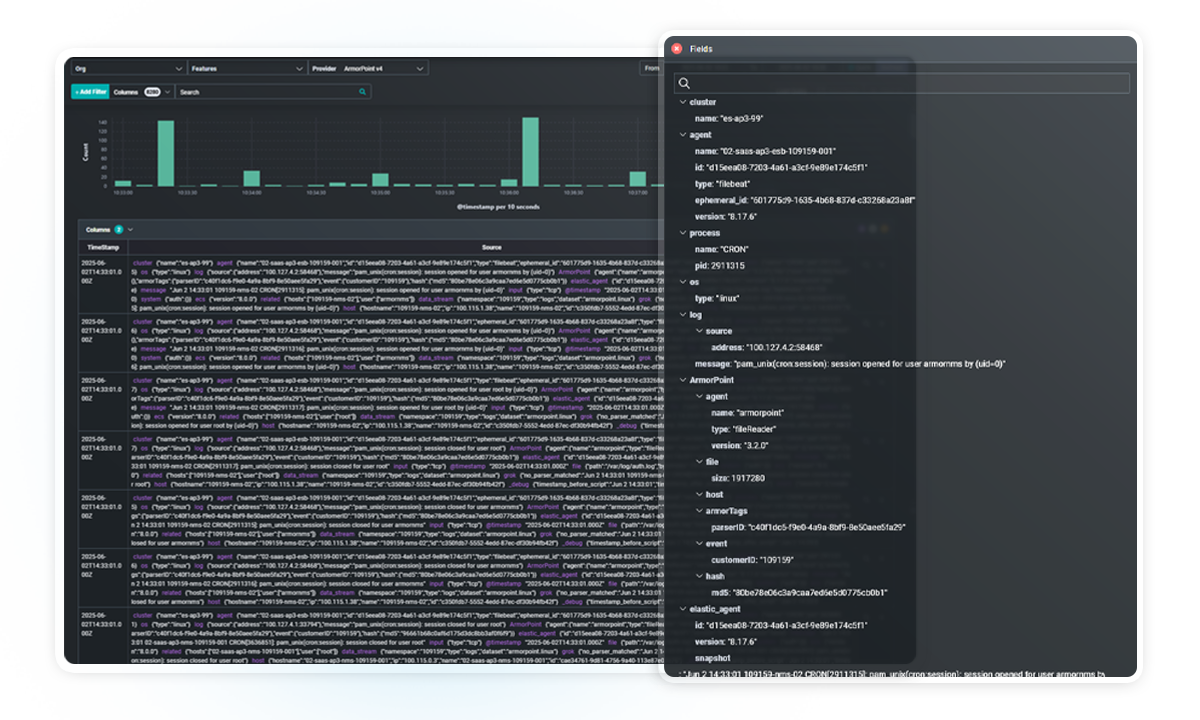
Key Features:
- Unlimited ingestion and retention of log files (hot and cold storage)
- Support for custom log types and formats (e.g., SSHGuard, IIS/Apache)
- Automatic parsing and normalization across data sources
- Searchable log archive with advanced filtering
- Integrated dashboards for KPI and anomaly visualization
Vulnerability Detection
Continuously assess assets for known vulnerabilities and misconfigurations. ArmorPoint identifies security gaps and prioritizes findings based on severity, exploitability, and relevance to your environment.

Key Features:
- Integration with vulnerability scanners and external asset data
- Mapping of CVEs to log and system activity
- Alerting on exposure to active exploit campaignsCustom rule creation for environment-specific threats
- Cross-correlation with threat intel for prioritization
- Audit reporting for patch management and remediation tracking
Incident Response
Support rapid investigation and coordinated response to threats. ArmorPoint’s managed SOC service includes incident triage and guidance to contain or mitigate threats before they escalate.

Key Features:
- Real-time alerting with SOC-led triage and escalation
- Incident tracking and timeline generation
- Recommendations for containment and remediation
- SLT-backed response procedures
- Integration with mobile app for on-the-go response
IT Hygiene
Maintain system integrity and enforce security best practices through continuous monitoring. ArmorPoint helps ensure proper configurations, user behaviors, and system policies are upheld across your infrastructure.
Key Features:
- Detection of insecure configurations and access anomalies
- Monitoring of dormant accounts, privileged access, and usage spikes
- Policy-based compliance validation (CIS benchmarks, NIST guidance)
- Automated alerts on misconfigured logging or disabled monitoring
- Environment-wide visibility for hygiene status reporting
Workload Protection
Extend detection and monitoring capabilities to cloud-native, hybrid, and on-prem workloads. ArmorPoint secures workloads against unauthorized access, suspicious activity, and privilege escalation.
Key Features:
- Log collection and correlation across VMs and cloud services
- Monitoring of lateral movement and inter-workload communication
- User activity auditing within workload boundaries
- Integration with AWS, Azure, and GCP environments
- Alerts on anomalous process execution or configuration drift
Posture Management
Continuously evaluate your organization’s security posture and reduce risk exposure through unified monitoring, detection, and compliance alignment.

Key Features:
- Centralized visibility into security operations and control gaps
- Customizable dashboards with posture metrics
- Event correlation tied to security policy violations
- Support for control assessments and audit preparation
- Ongoing alignment with internal governance and external frameworks
Threat Intelligence
Enhance detection accuracy and accelerate response with built-in threat intelligence. ArmorPoint enriches every event with context from commercial and open-source feeds, giving security teams the intel they need to prioritize and respond with confidence without additional licensing or subscription costs.
Key Features:
- Integration of multiple commercial and open-source threat intelligence feeds
- Automatic enrichment of logs and alerts with IOCs, IP reputation, malware signatures, and more
- Real-time correlation between internal events and external threat indicators
- Support for threat scoring, tagging, and prioritization
Built for Visibility. Backed 24×7 by Humans. Delivered as a Service.
Security that sees deeper, so you can act faster.
Don't Rip and Replace. Integrate.
Seamlessly integrate the tools your customers already trust with ArmorPoint to achieve unparalleled visibility and control over security operations – all from a single, unified platform.
Frequently Asked Questions
What kind of correlation can ArmorPoint perform?
We use behavior- and rule-based correlation to detect lateral movement, privilege escalation, exfiltration, and more, across your environment.
What’s included in incident response?
Our SOC handles triage, containment recommendations, and initial response actions. All included—no surprise charges.
How fast is your response time?
Our SOC team operates under defined SLTs available in your service agreement.
Do I need to configure log sources manually?
Once our agent is installed, we help configure audit policies and parsing rules to ensure complete visibility.






