In the past year alone, 83% of organizations reported insider attacks, highlighting a concerning issue in cybersecurity: the increasing complexity and difficulty in detecting such threats. Traditional defenses are proving less effective against the sophisticated tactics now used in insider attacks, compounded by the sheer volume of data in modern networks. This is where User and Entity Behavior Analytics (UEBA) comes into play. By analyzing the behavior of users and entities within an organization, UEBA can detect unusual activities that traditional tools might miss.
User and Entity Behavior Analytics (UEBA) Explained
User and Entity Behavior Analytics (UEBA) is a cybersecurity solution that leverages machine learning, analytics, and data aggregation to monitor and analyze the behavior of users (employees, contractors) and entities (devices, applications, servers) within an organization.
Instead of relying solely on predefined rules, UEBA identifies what is “normal” for each user or entity and flags any behavior that deviates from this baseline. This dynamic approach is particularly effective at uncovering insider threats, compromised accounts, and other subtle security risks that might go unnoticed with traditional tools.
How Does UEBA Work?
UEBA works by collecting data from multiple sources across your IT environment, such as:
- Activity Logs: Login attempts, file access, and network usage
- Security Tools: SIEM solutions, firewalls, and antivirus software
- Directory Services: User profiles and access permissions
Using this data, UEBA establishes a baseline of normal activity for each user and entity. Advanced analytics and machine learning continuously monitor and compare current behavior to the baseline. When anomalies—such as accessing unusual files, logging in at odd hours, or excessive data transfers—are detected, the system generates alerts for further investigation.
Benefits of UEBA
Integrating UEBA into your cybersecurity strategy offers several advantages:
- Proactive Threat Detection: UEBA identifies suspicious behavior patterns, such as insider threats or compromised accounts, before they cause damage.
- Improved Accuracy: Machine learning reduces false positives by distinguishing between legitimate and suspicious activities more effectively than static rule-based systems.
- Enhanced Incident Response: Real-time alerts enable faster investigation and remediation of potential threats.
- Adaptability: UEBA evolves with your organization, learning and adapting as user and entity behaviors change over time.
- Regulatory Compliance Support: By providing detailed insights into user activities, UEBA helps meet compliance requirements like GDPR, HIPAA, and PCI DSS.
UEBA Use Cases
UEBA can be applied in a variety of scenarios to strengthen your organization’s security posture. Some of the most common use cases include:
- Insider Threat Detection: Identifying when an employee accesses sensitive data they don’t typically interact with or exfiltrates information.
- Compromised Accounts: Detecting unusual login patterns or unauthorized access using legitimate credentials.
- Fraud Prevention: Uncovering fraudulent activities, such as unauthorized transactions or changes in financial systems.
- Privileged Account Monitoring: Keeping tabs on high-level users to ensure their credentials aren’t being abused or misused.
- Data Exfiltration Prevention: Recognizing large or unauthorized data transfers before critical information is lost.
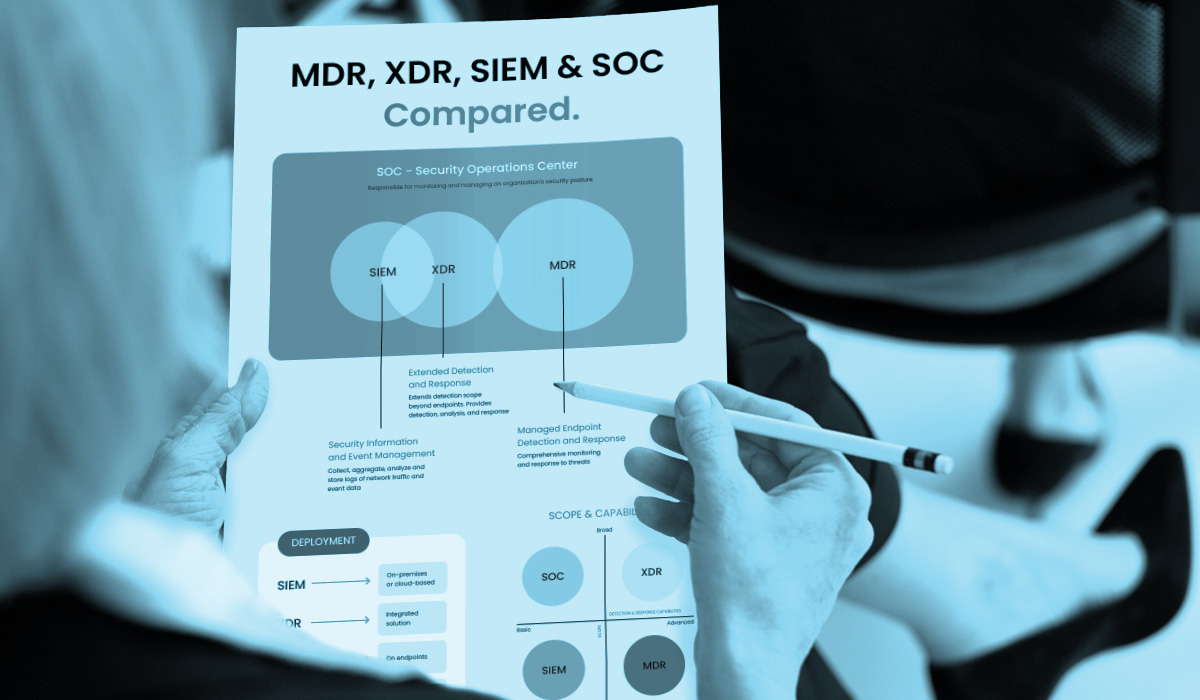
XDR vs EDR vs UEBA
XDR (Extended Detection and Response), EDR (Endpoint Detection and Response), and UEBA (User and Entity Behavior Analytics) each address different cybersecurity needs. EDR focuses on real-time threat detection at the device level, monitoring and mitigating endpoint-specific threats like malware. XDR expands this scope by integrating data from networks, clouds, and endpoints for a comprehensive security overview, enhancing overall threat detection and response. In contrast, UEBA analyzes behaviors of users and entities to identify subtle anomalies that signal potential security threats, such as insider threats or compromised credentials, which traditional systems might miss. Together, these solutions form a layered defense, each enhancing aspects of an organization's cybersecurity framework.
UEBA vs SIEM
SIEM (Security Information and Event Management) systems compile and analyze security data but typically depend on fixed correlation rules that struggle to keep up with dynamic security landscapes. On the other hand, UEBA adopts a behavior-focused approach that enhances the precision of threat detection. This reduces dependence on static rules that may not capture the complexities of advanced threats, ensuring more adaptable and effective security monitoring.

How ArmorPoint Managed SOC Utilizes UEBA
ArmorPoint’s 24/7 Managed SOC services seamlessly integrates UEBA, SIEM, EDR and SOC to provide continuous monitoring and detailed analysis of user and entity behaviors. This proactive approach helps predict and prevent security incidents before they escalate, ensuring that your organization remains resilient against both internal and external threats. Ready to enhance your cybersecurity? Learn how ArmorPoint can help you future-proof your security operations strategy with our Managed SOC services.