TL;DR
The Payment Card Industry Data Security Standard (PCI DSS) v4.0.1, effective March 2025, requires organizations handling card data to adopt a customizable approach to compliance. This version emphasizes continuous security vigilance, enhanced reporting, and updated requirements to address modern threats like broader network controls and strong encryption.
Since its introduction in 2004, the Payment Card Industry Data Security Standard (PCI DSS) has been pivotal in shaping secure payment environments. Governed by the PCI Security Standards Council (PCI SSC), this standard ensures that entities involved in payment card processing, storage, or transmission maintain robust security measures. As cyber threats evolve and payment technologies advance, PCI DSS has been continually updated to address new security challenges, with the latest iteration being version 4.0.1.
The Evolution of PCI DSS
PCI DSS was initially established to create a unified security standard across the diverse entities handling payment card data. Over the years, it has been revised to address the shifting landscape of cybersecurity threats and technology developments. Each version aims to close security gaps from its predecessors and introduces more stringent requirements, with version 4.0.1 being the most comprehensive, incorporating modern cybersecurity methodologies.
What's New in PCI DSS v4.0.1?
Released in June 2024, PCI DSS v4.0.1 is a limited revision to the major overhaul introduced in PCI DSS v4.0. This update primarily addresses feedback from stakeholders and clarifies existing requirements rather than introducing new ones. While the core enhancements were laid out in version 4.0, which introduced significant changes including 64 new requirements, version 4.0.1 focuses on refining these updates through minor corrections and improved guidance. This includes fixing typographical errors, aligning the language more closely with user feedback, and providing clearer instructions on compliance expectations. As of December 31, 2024, PCI DSS v4.0 will be retired, making v4.0.1 the standard for maintaining secure payment environments.
Key Updates in PCI DSS 4.0
The introduction of PCI DSS v4.0 in 2022 marked a significant evolution in the standard, addressing emerging cyber threats and providing a flexible framework to accommodate varying technological landscapes, while PCI v4.0.1 builds on these updates by refining and clarifying the standards to ensure better compliance and security. Let’s review the key updates in PCI DSS v4.0 to understand the updated requirements ahead of the March enforcement date.
Customizable Approach to Compliance
To support innovation in payment technology and to accommodate various organizational methods, PCI DSS v4.0 offers increased flexibility in achieving compliance objectives. This includes the allowance of group, shared, and generic accounts, and targeted risk analyses that allow organizations to determine how frequently certain security tasks should be performed. This flexibility supports the customized approach, enabling organizations to use innovative methods to meet security objectives effectively.
Increased Focus on Continuous Security
Recognizing that threats are continuous, PCI DSS v4.0 emphasizes the need for ongoing security vigilance. This is supported through clearly defined roles and responsibilities for security maintenance and additional guidance to help organizations implement and sustain security measures effectively.
Enhanced Validation and Reporting Procedures
To enhance the integrity of compliance reporting, PCI DSS v4.0 improves the alignment between the information reported in a Report on Compliance (RoC) or Self-Assessment Questionnaire (SAQ) and the summaries provided in an Attestation of Compliance. This change aims to support better transparency and granularity in reporting, ensuring stakeholders have a clear view of an organization's compliance status.
Who Does PCI DSS v4.0.1 Apply To?
PCI DSS v4.0.1 applies to all entities involved in storing, processing, or transmitting cardholder data (CHD) and sensitive authentication data (SAD), as well as those that could affect the security of CHD and SAD. This includes a wide range of entities within the payment ecosystem, such as merchants, payment processors, acquirers, issuers, and service providers. Compliance with PCI DSS is managed by organizations that oversee payment security, including payment brands and acquirers. These organizations determine the necessity and extent of compliance and validation for each entity. For specific compliance requirements and any additional criteria, entities should directly consult with the relevant managing organizations.
PCI v4.0.1 Compliance Timeline
The shift to PCI v4.0.1 began with its official release in 2022, with a grace period allowing organizations to adapt to the new standards through a phased approach. By March 31, 2025, all entities must fully comply with the new requirements. This phased approach helps organizations gradually update and test their security systems without disrupting ongoing operations.

Cost of Non-Compliance
Failing to comply with PCI DSS v4.0.1 can result in various severe consequences for businesses, including:
- Financial Penalties: Initial fines range from $5,000 to $100,000 per month, increasing with prolonged non-compliance
- Operational Impacts: Potential suspension or revocation of payment processing abilities, significantly disrupting business operations
- Remediation Costs: Legal fees, forensic investigation costs, credit card replacement, and fraud reimbursements can accumulate, especially following a data breach
- Reputation Damage: Loss of customer trust and loyalty after a data breach, leading to long-term financial losses
Updates to the 12 Core PCI DSS Requirements
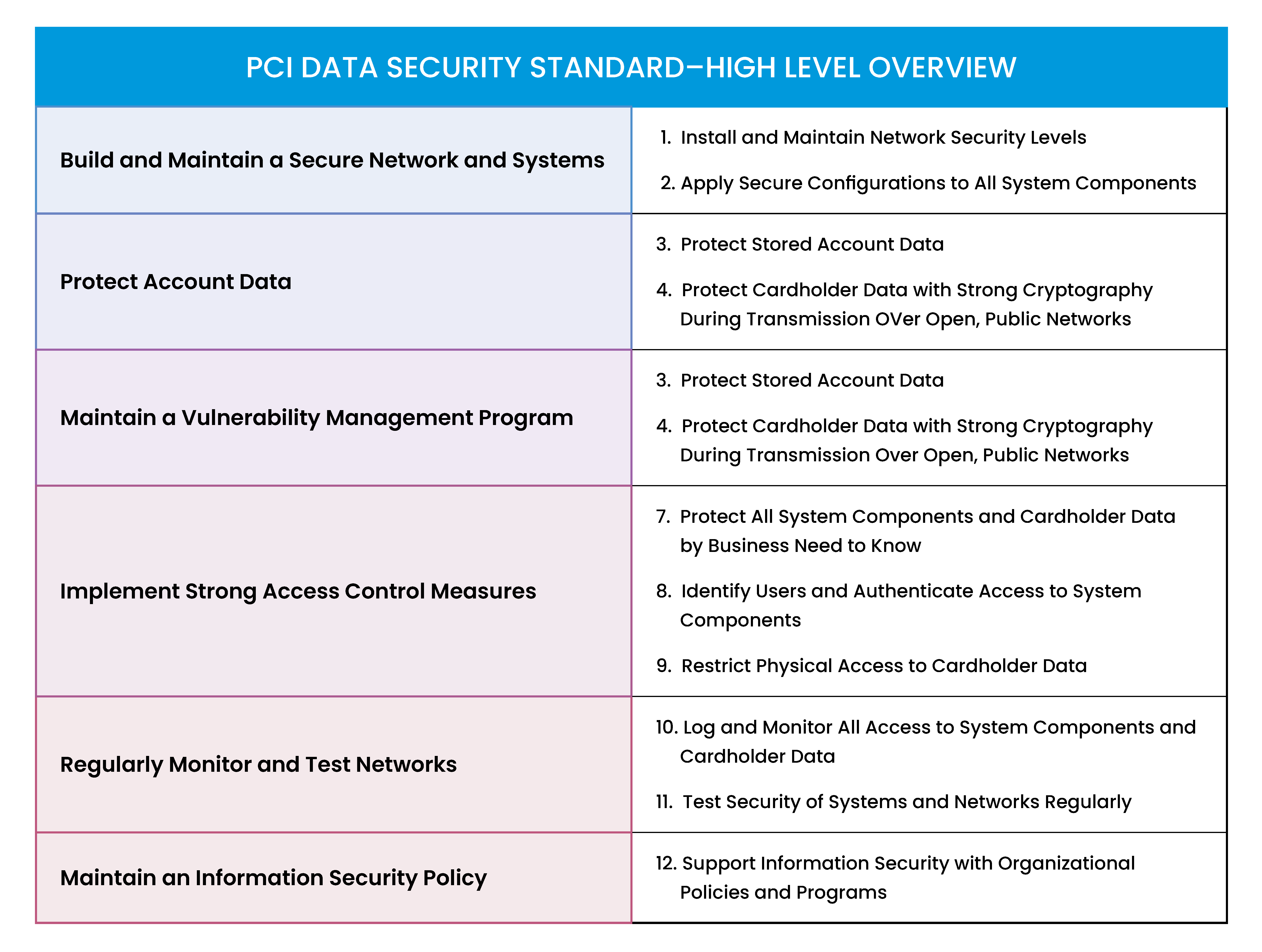
PCI DSS 4.0 Requirement 1: Install and Maintain Network Security Controls
PCI DSS 4.0 shifts the focus from traditional firewalls to a broader framework of Network Security Controls (NSC). This strategic move allows organizations greater latitude in configuring their security setups to protect against external threats and untrusted networks, while still ensuring robust defense mechanisms are in place.
PCI DSS 4.0 Requirement 2: Apply Secure Configurations to All System Components
PCI 4.0 advises against using vendor-supplied defaults for any network devices, applications, or systems. Instead, organizations are encouraged to adopt custom configurations that enhance security measures beyond the predictable and often weak factory settings in order to reduce vulnerabilities.
PCI DSS 4.0 Requirement 3: Protect Stored Account Data
This requirement mandates the encryption and secure management of stored account and cardholder data. Emphasis is placed on employing tokenization to replace sensitive data elements like the Primary Account Number (PAN) with unique identifiers, minimizing the impact of potential data breaches.
PCI DSS 4.0 Requirement 4: Protect Cardholder Data with Strong Cryptography During Transmission Over Open, Public Networks
PCI 4.0 requires that any cardholder data used during transactions, such as recurring payments, be encrypted. This is crucial for protecting data as it moves through various network points, which are frequent targets for cyber-attacks.
PCI DSS 4.0 Requirement 5: Protect All Systems and Networks from Malicious Software
Businesses are encouraged to incorporate advanced anti-malware technologies, including AI and ML-based tools, into their security strategies. Regular updates and maintenance of these systems are essential to keep up with evolving malware threats.
PCI DSS 4.0 Requirement 6: Develop and Maintain Secure Systems and Software
PCI 4.0 expands its focus to include maintaining the security of all software used in the payment process. This involves regular updates, application of security patches, and the use of Web Application Firewalls (WAF) to combat web-based threats.
PCI DSS 4.0 Requirement 7: Restrict Access to System Components and Cardholder Data by Business Need to Know
Access to cardholder data must be tightly controlled and limited to individuals whose job roles require it. This minimizes internal threats and ensures that sensitive information is only accessible on a need-to-know basis.
PCI DSS 4.0 Requirement 8: Identify Users and Authenticate Access to System Components
This requirement emphasizes the need for strong, multi-factor authentication for all users accessing cardholder data. Unique user IDs and stringent authentication processes help track access and enhance overall data security.
PCI DSS 4.0 Requirement 9: Restrict Physical Access to Cardholder Data
Managing physical access to sensitive cardholder data involves controlling entry to data storage sites and utilizing surveillance measures like CCTV to monitor these areas, ensuring that only authorized personnel have access.
PCI DSS 4.0 Requirement 10: Log and Monitor All Access to System Components and Cardholder Data
Organizations are required to implement detailed logging and monitoring of all access to network resources and cardholder data. Automated log reviews and real-time alerts for security incidents are crucial components of this requirement.
PCI DSS 4.0 Requirement 11: Test Security of Systems and Networks Regularly
Regular testing of security systems and processes is mandated to identify and rectify vulnerabilities. This includes performing vulnerability scans and penetration tests to ensure defenses remain effective against new threats.
PCI DSS 4.0 Requirement 12: Support Information Security with Organizational Policies and Programs
The final requirement focuses on supporting information security through comprehensive organizational policies and programs. It involves conducting targeted risk analyses to back each PCI DSS requirement, documenting cryptographic protocols, and reviewing hardware and software technologies, ensuring that all components contribute to a secure payment processing environment.
Conclusion
With the introduction of PCI DSS v4.0, organizations are equipped with updated guidelines that address the latest security challenges and threats. It is essential for businesses to not only understand these changes but to integrate them into their cybersecurity strategy to continue to safeguard sensitive payment data effectively.
For comprehensive guidance and resources on PCI DSS compliance, visit the PCI Security Standards Council’s document library. To ensure you are always ahead of compliance requirements and leveraging the best practices in payment security, subscribe to ArmorPoint Insights.










