TL;DR
The validation stage of a Continuous Threat Exposure Management (CTEM) framework is crucial for a proactive security posture. It involves using a combination of vulnerability scanning, expert penetration testing, and automated breach and attack simulations (BAS) to continuously test and validate the effectiveness of security controls.
The increasing complexity and frequency of cyber threats have driven organizations to adopt Continuous Threat Exposure Management (CTEM) to maintain a robust security posture. Traditional, periodic security assessments are no longer sufficient in an environment where new vulnerabilities and attack techniques emerge constantly. CTEM provides a proactive and continuous approach to threat management, enabling organizations to stay ahead of potential threats and reduce their overall risk.
5 Stages of CTEM
- Scoping and Planning: Define the objectives and scope of the CTEM program, identify key assets, and establish a security baseline.
- Discovery and Inventory: Inventory all assets, including hardware, software, and data, and map the network to understand system interdependencies.
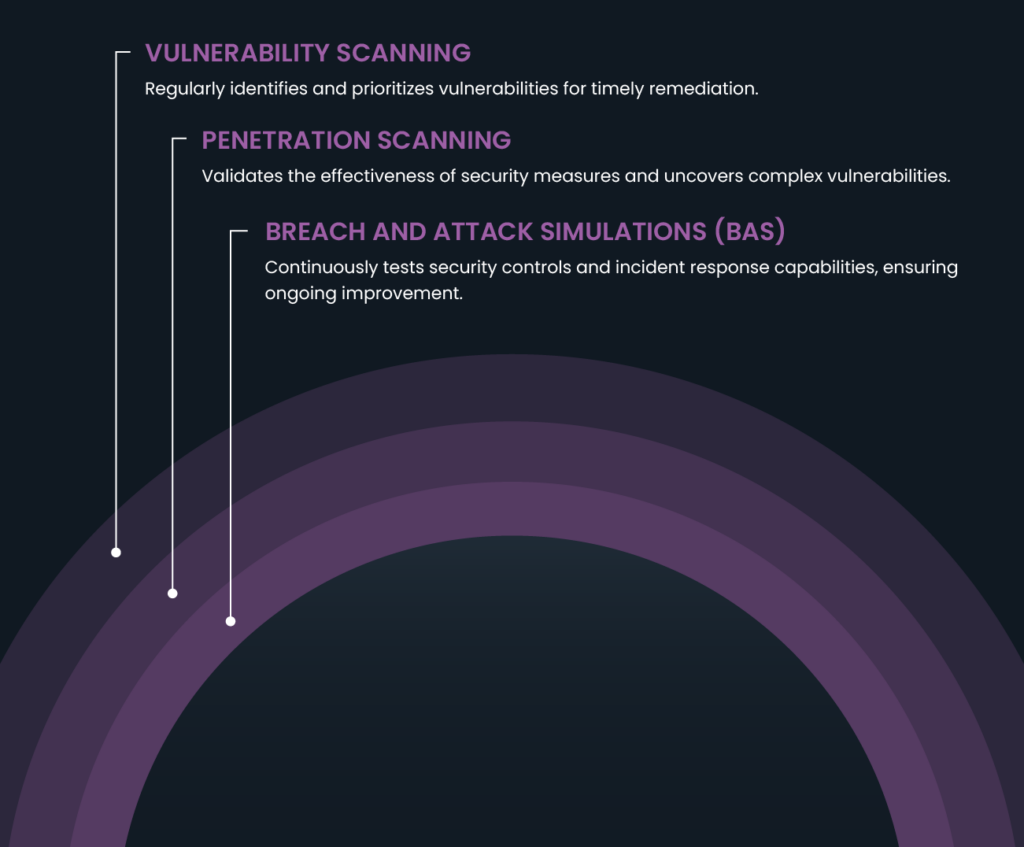
- Validation: Use vulnerability scanning, penetration testing, and breach and attack simulations (BAS) to identify and validate vulnerabilities, test security controls, and simulate attack scenarios.
- Remediation and Mitigation: Prioritize and implement remediation efforts, such as patching vulnerabilities and enhancing security controls based on validation findings.
- Continuous Monitoring and Improvement: Establish ongoing monitoring to track the effectiveness of security measures, detect new threats, and continuously improve the security posture.
Mastering Stage 3 of CTEM: Vulnerability Scans vs Penetration Tests vs Breach and Attack Simulations
Validation is the critical bridge between identifying potential vulnerabilities and taking concrete actions to mitigate them. Before organizations can effectively remediate and mitigate threats, they must first confirm their existence and understand their potential impact. This is achieved through a series of proactive tests that thoroughly assess the security environment, revealing weaknesses and validating the effectiveness of existing security controls. Mastering the Validation stage is essential for ensuring that the efforts in subsequent stages of CTEM are both targeted and effective. Let’s explore the tests that your organization can run to validate vulnerabilities.
Understanding Vulnerability Scanning
What is Vulnerability Scanning?
Vulnerability scanning is an automated process that identifies known vulnerabilities in an organization's systems, networks, and applications. This process involves using specialized tools to scan for security weaknesses that could potentially be exploited by attackers.
How does Vulnerability Scanning Work?
The vulnerability scanning process typically involves the following steps:
- Asset Identification: The scanner identifies and inventories all devices, systems, and applications within the network.
- Scanning: The tool performs a systematic scan of the identified assets, checking for known vulnerabilities such as outdated software, misconfigurations, and missing patches.
- Analysis: The scan results are analyzed to determine the severity and potential impact of the identified vulnerabilities.
- Reporting: A detailed report is generated, highlighting the discovered vulnerabilities and providing recommendations for remediation.
What are the Benefits of Vulnerability Scanning?
- Early Detection: Regular scanning helps organizations detect vulnerabilities early, allowing for timely remediation before they can be exploited.
- Vulnerability Prioritization: Vulnerability scanning tools often include risk scoring, enabling organizations to prioritize vulnerabilities based on their severity and potential impact.
Vulnerability Scanning and Continuous Threat Exposure Management
Regular vulnerability scanning is a cornerstone of an effective CTEM program. By continuously identifying and prioritizing vulnerabilities, organizations can take proactive measures to remediate them, reducing the risk of exploitation. This ongoing process ensures that security teams are always aware of their security posture and can address weaknesses promptly.
Understanding Penetration Testing
What is Penetration Testing?
Penetration testing, or pen testing, is a simulated cyberattack performed by security experts to identify and exploit vulnerabilities in an organization's systems. The goal is to uncover security weaknesses that could be used by attackers to gain unauthorized access.
How Does Penetration Testing Work?
The pen testing process typically involves the following phases:
- Planning: Define the scope and objectives of the test, including which systems will be tested and the rules of engagement.
- Reconnaissance: Gather information about the target systems to identify potential entry points.
- Scanning: Use automated tools to scan for vulnerabilities.
- Exploitation: Attempt to exploit identified vulnerabilities to gain access to systems and data.
- Reporting: Document the findings, including the vulnerabilities discovered, the methods used to exploit them, and recommendations for remediation.
What are the benefits of Penetration Testing?
- Uncovering Complex Vulnerabilities: Pen testing can identify complex and hidden vulnerabilities that automated tools might miss.
- Actionable Insights: Provides detailed insights into how an attacker could exploit vulnerabilities and the potential impact on the organization.
What are the types of penetration tests?
- Manual Pen Testing: Conducted by skilled security professionals, manual pen testing is thorough and can uncover nuanced vulnerabilities. However, it is time-consuming and resource-intensive.
- Automated Pen Testing: Uses automated tools to conduct tests, providing quicker results but potentially missing more complex vulnerabilities.
Penetration Testing and Continuous Threat Exposure Management
Penetration testing provides a deeper understanding of an organization's security weaknesses and validates the effectiveness of security measures. By uncovering and addressing these vulnerabilities, organizations can enhance their overall security posture, making pen testing an integral part of a comprehensive CTEM strategy.
Understanding Breach and Attack Simulations (BAS)
What is Breach and Attack Simulations?
Breach and Attack Simulations involve using automated tools to simulate advanced attack scenarios on an organization's systems. The objective is to continuously test and evaluate the effectiveness of security controls and incident response mechanisms.
How Do Breach and Attack Simulation Tools Work?
BAS tools operate by:
- Simulating Attacks: These tools mimic real-world attack techniques used by cybercriminals.
- Testing Security Controls: BAS tools test the organization's security controls and defenses against these simulated attacks.
- Evaluating Responses: The tools assess how effectively the organization can detect, respond to, and mitigate these simulated attacks.
What are the benefits of Breach and Attack Simulations?
- Continuous Assessment: Provides ongoing evaluation of security controls and incident response capabilities.
- Improved Incident Response: Helps organizations identify gaps in their incident response processes and improve their readiness to handle actual attacks.
- Enhanced Security Posture: Continuously validates the effectiveness of security measures, ensuring they are always up to date and capable of defending against advanced threats.
Breach and Attack Simulations and Continuous Threat Exposure Management
BAS provides ongoing insights into an organization's readiness to detect and respond to attacks, ensuring continuous improvement of security controls and incident response capabilities. By incorporating BAS into a CTEM program, organizations can maintain a proactive stance against emerging threats.
Integrating Vulnerability Scanning, Pen Testing, and BAS in CTEM
Integrating vulnerability scanning, pen testing, and BAS is crucial for a comprehensive CTEM strategy. Each tool provides unique insights and benefits, creating a multi-layered defense approach that ensures continuous visibility and protection against threats.
By combining these tools, organizations can achieve a holistic view of their security posture, enabling them to proactively address vulnerabilities and enhance their defenses against cyber threats.
Conclusion
Maintaining a robust security posture requires a proactive and continuous approach. Integrating vulnerability scanning, penetration testing, and breach and attack simulations into a Continuous Threat Exposure Management (CTEM) framework is essential for identifying, prioritizing, and mitigating vulnerabilities effectively. These tools complement each other, providing a multi-layered defense strategy that ensures continuous visibility and protection against threats.
Explore our comprehensive Managed Risk solutions today to start implementing a CTEM framework and enhance your organization's cybersecurity posture.








